EntraID on the Modernisation Platform
What is EntraID?
EntraID (formerly Azure AD) is the Ministry of Justice enterprise identity provider used for all justice.gov.uk accounts, email, and core applications such as Word and Excel. It manages user identities linked to @Justice accounts, provides authentication and group-based access control, and forms part of the core infrastructure for the Ministry of Justice.
How the EntraID integration works
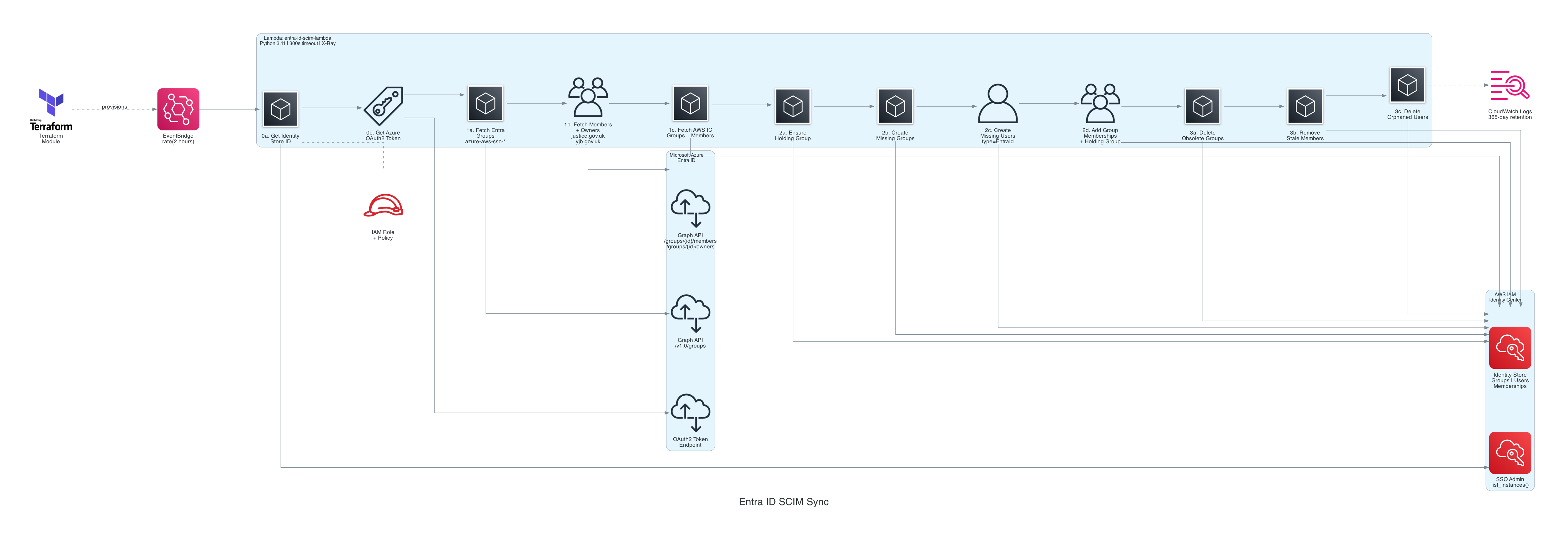
EntraID is the authoritative source for user identities and core groups. AWS IAM Identity Center consumes those identities to grant access to AWS accounts and permission sets. The platform uses SCIM sync jobs to reconcile EntraID group membership into Identity Center, so access is kept consistent across MoJ identities. This design means access changes flow from enterprise identity through to AWS, while platform automation keeps memberships aligned.
Troubleshooting and maintenance
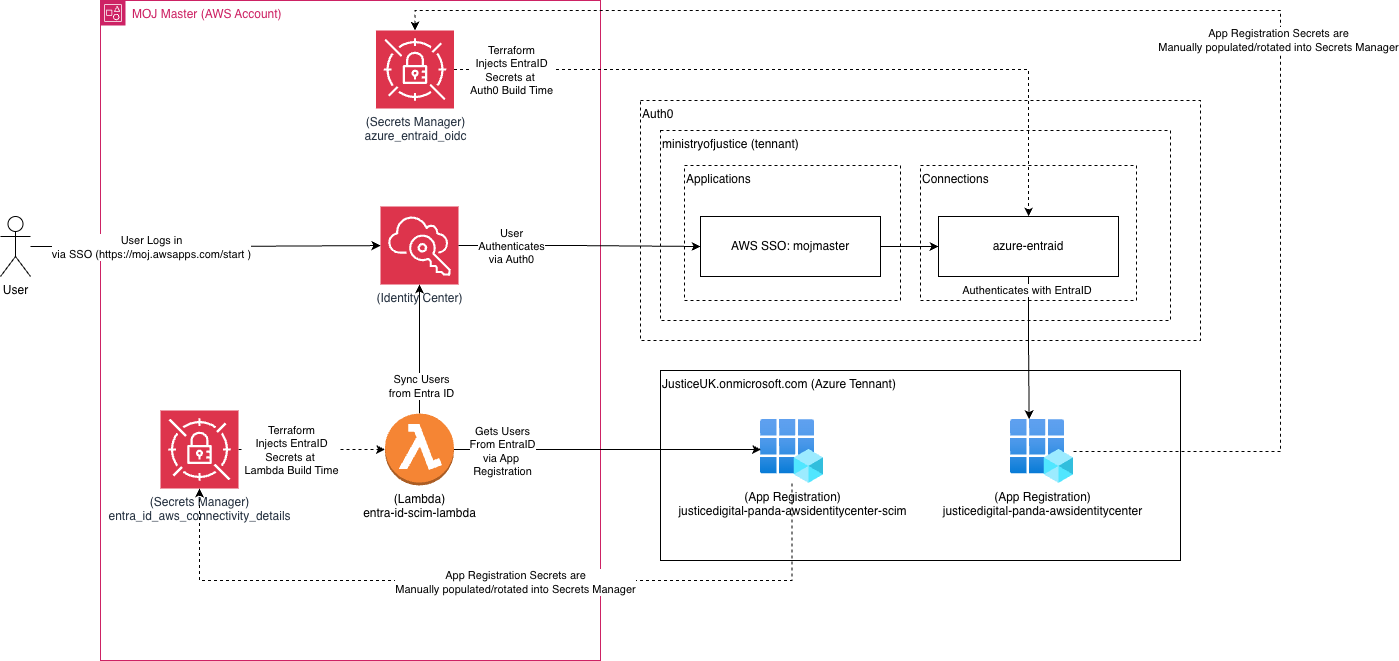
This section covers the high-level architecture of the EntraID integration, the key components, and how they interact, plus common maintenance tasks. Because the integration uses secrets in the Lambda job, these must be rotated every 90 days. The rotation process is manual and involves creating new secrets in the Azure application manager, updating the AWS secret in Secrets Manager in the AWS root account, and then testing the integration to ensure it continues to function correctly. The diagram below shows how the components interact and where the secrets are used.
Currently the rotation process is manual, but there are plans to automate it to reduce operational overhead and ensure secrets are rotated on time.
For SCIM job schedules, secrets, troubleshooting, and manual execution steps, see the SCIM Lambda runbook.
Why we use it
The Modernisation Platform has adopted EntraID as an identity provider for AWS account access and management. This decision was driven by several key factors:
- Supports non-developer users and enterprise identity requirements
- Aligns access management with MoJ identity standards
- Enables consistent onboarding and offboarding across services
Authentication and access flow
User authentication with AWS via Auth0, which has another app on EntraID. This process is separate from the SCIM sync, so has its own secrets and rotation process, but is also a critical part of the overall integration and user access flow.
Authentication uses EntraID for MoJ identities and AWS IAM Identity Center for account access. For more detail on logging in and the user experience, see the Single Sign-On guide.
Group and access management
Currently the management of group membership is split between GitHub and EntraId, with the intention to move towards more of a single source of truth in EntraId over time. and as such, the current model is:
- Group membership controls access to AWS accounts and roles
- EntraId group creation currently needs approval controls
Both the GitHub and EntraId groups are created outside of the Modernisation Platform. Anyone with permission to create
EntraId groups can create a new group, and it will be added to AWS as long as the group name starts
with azure-aws-sso. The platform's role is to consume those groups and manage access in AWS.
For more information about group permission and how groups are given permissions to AWS accounts, see the following documentation: Platform User Roles
Auth0 access and integration
Auth0 sits between EntraID and AWS IAM Identity Center as the authentication broker for the user login flow. It uses an EntraID app registration to authenticate MoJ users and then issues the tokens used for AWS access. This Auth0 integration is separate from the SCIM sync process and has its own secrets and rotation cycle, but it is a critical part of the end-to-end access path.
Ownership and support
- Owned by the Modernisation Platform team
- Built in collaboration with Hosting Leads
Related documentation
Was this page useful?